Kashmiris use VPN to skirt internet curbs. But is VPN really secure?
All VPN providers say they offer complete security and anonymity. That's not entirely accurate.
In preparation for dismantling Jammu and Kashmir’s autonomy last August, the Indian government imposed a communications blackout in the erstwhile state, snapping phone and internet connectivity. Phone services were gradually restored over the following months but mobile internet wasn't turned back on until January 2020. When it was, it was severely restricted.
Initially, just over 300 websites “whitelisted” by the government were accessible, that too only on slower 2G internet. Most social media platforms and video streaming services were not on the whitelist.
On Wednesday, while curbs on the use of social media were finally lifted after seven full months, mobile internet continues to be restricted to 2G speed. The respite may be temporary though, given the authorities have said the decision to remove the restrictions would be reviewed on March 17.
Kashmiris might yet have to go back to using Virtual Private Networks, or VPNs. It's a risky endeavour: that Kashmiris were employing VPNs to skirt the internet restrictions had not gone down well with the authorities.
According to a report by Scroll, security forces initially "resorted to physical checks of smartphones" and subsequently the police filed an FIR "on the alleged misuse of social media through VPNs". There have been "at least five cases of arrest since February 17, all for social media and VPN use", the report states.
So, what’s VPN and how does it work? Here’s an explainer.
How do we connect to the internet?
When your computer or mobile phone or TV is connected to the internet, it’s assigned an Internet Protocol, or IP address. It’s the address from which requests are sent to the servers of websites you visit and to which the servers send the requested data, such as a webpage or a video or an image. It’s quite like your physical address except that everytime you connect to the internet, your IP address might change.
So, what can we glean from your IP address? It contains information about your internet service provider – say, Airtel, Vodafone, Jio – your city, postal code, and your approximate location based on latitude and longitude.
Where does VPN come in?
A Virtual Private Network is basically a series of servers that masks your real IP address by substituting it with a fake one. It sits between your computer and the website server that you are accessing, thus rerouting internet traffic. To ensure you are not identified from the data you send or receive, the VPN encrypts and decrypts the data packets passing through it. It’s like sending or receiving mail that can’t be opened by a third party.
Let’s assume you are in Kashmir and your IP address is 105.40.223.183. You need to access Google but the website is blocked in Kashmir. So, you install a VPN. The VPN will send a request to Google’s servers telling them your IP address is 22.189.183.130. That is in Kansas, US. Since Google isn’t banned in Kansas, its servers will send the requested data to the VPN, which in turn will send it to your computer. Google’s servers won’t know the request for data originated in Kashmir.
Are VPNs freely available?
A few companies provide their VPN services for free. For others, you have to pay.
There are two ways to use VPN and both might cost you.
One, you can pay a VPN company to use their services. They have network infrastructure across the world and you can choose which server to connect to. All your internet traffic will pass through that server.
Two, you can create a VPN on your own. This involves setting up a server, and working out server and network configurations. If any problems arise, you would need to fix them yourself.
Is technical expertise needed to use VPN?
Not if you use the services of a VPN provider. If you want to set up your own server then, obviously, you would require some technical knowledge. However, YouTube has plenty of tutorials about setting up a VPN and fixing problems that might arise. So, if you’re dedicated enough, you can set up a VPN on your own even if you do not have much technical expertise. In the context of Kashmir, a journalist who is somewhat tech savvy can set up a VPN and help fellow mediapersons connect to this network.
Can a VPN user be tracked?
All VPN providers say they offer complete security and anonymity. That's not entirely accurate. Internet service providers broadly know if you are using VPN.
VPN providers advertise using “military-grade encryption”. But all modern web browsers employ such encryption by default.
VPN providers say they don’t keep logs of a user’s activity. But they have to keep some activity logs, and even hand them over if law enforcement authorities seek them through lawful means such as court subpoenas.
Spy agencies, such as America’s NSA, are known to keep track of people who search for keywords related to VPN. So, if you search for such keywords, you might become a target of surveillance.
So, is there no way to stay completely anonymous?
Well, there is. Here’s a primer.
If you are using Windows OS, stop running Microsoft Internet Explorer and Microsoft Edge browsers.
Uninstall Chrome and Mozilla browsers.
Install Tor on your computer or phone. Then use its inbuilt web browser for all your work.
This will safeguard your identity online without you having to pay for VPN subscriptions. Using Tor is somewhat different from using VPN servers. But if your Windows operating system itself is infected or compromised in some way, then even this isn’t a completely secure way of accessing the internet.
So, what can you do?
Install the OS which the whistleblower Edward Snowden used to escape NSA’s surveillance. It’s called the Tails OS, a privacy-focussed system built upon the Linux kernel and made specifically for use with the Tor network. All its incoming and outgoing connections are forced to go through the Tor network. All of the OS code is open source, so we know there are no security vulnerabilities in it. And it works entirely on the computer’s RAM; nothing is stored by the OS on the hard disk.
Here’s what you need to do to use Tails OS:
Buy a new pendrive with at least 8 GB storage space.
Download Tails OS on the pendrive.
Restart your computer.
In BIOS settings, change the boot sequence to boot first from your pendrive instead of your hard disk.
Your Tails OS will boot up now. It offers a minimal desktop environment and you can use the inbuilt web browsers as usual.
The overall experience of using the internet will be significantly slower but you can be assured that you are completely anonymous.
Once you are done with your work, shut down your machine and take out the pendrive. It will not leave any digital footprint on the machine.
You can carry your pendrive with you and securely use any machine without worrying about security and privacy.
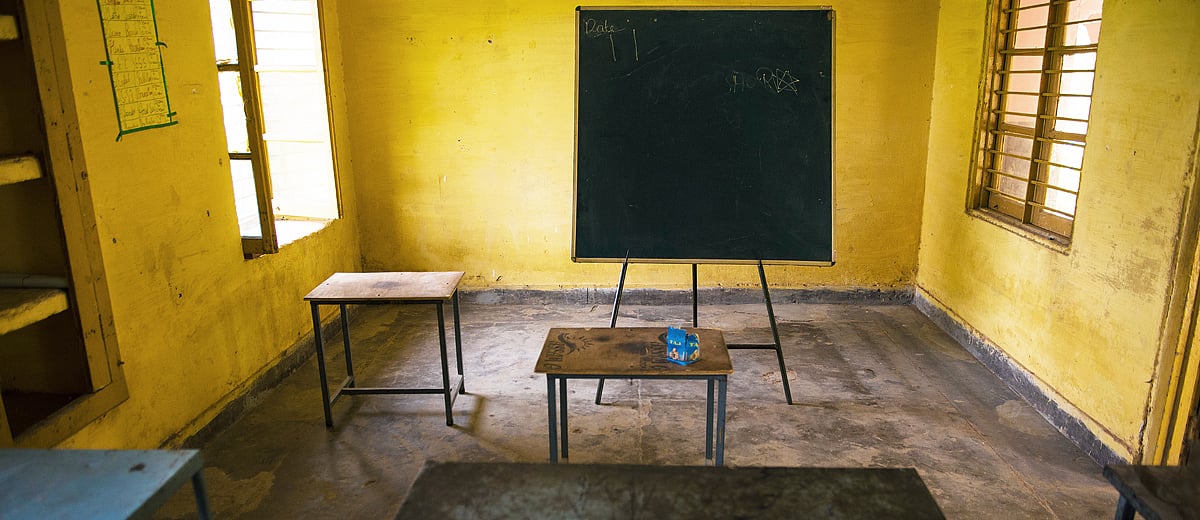 No school, no Internet is the ‘new normal’ for students in Kashmir
No school, no Internet is the ‘new normal’ for students in Kashmir Pendrives & gumption: How journalists in Kashmir are dealing with communications blockade
Pendrives & gumption: How journalists in Kashmir are dealing with communications blockade